The way organizations think about security has changed forever. Remote work, multi-cloud environments, and mobile access have dissolved the boundaries that once defined the traditional network perimeter.
Attackers no longer need to break through the firewall—they simply log in with stolen credentials or exploit weak internal defenses.
This shift has exposed a harsh truth: perimeter-based security can’t keep up with today’s distributed networks and user behaviors.
That’s where Zero Trust Security comes in. Instead of assuming trust based on location or network, Zero Trust operates on one rule — never trust, always verify. Every user, device, and request is authenticated continuously, no matter where it originates.
In this guide, you’ll learn what defines a strong Zero Trust provider, how ZTNA works, and which vendors are leading the way today.
What Makes a Zero Trust Provider Worth Considering?
Choosing the right Zero Trust provider means more than checking off a few security boxes. The foundation of Zero Trust lies in strict identity verification, granular access control, and continuous monitoring—but how each provider enables these can vary widely.
Start with the essentials:
- Zero Trust Network Access (ZTNA)
This is the core of any Zero Trust solution. ZTNA ensures users access only specific resources, not the entire network. It reduces lateral movement and limits the scope of a breach. - Identity and Access Management (IAM)
A good provider should support robust IAM features, allowing you to verify user identity before access is granted. Integration with leading identity providers (like Okta, Microsoft, or Google) is a plus. - Multi-Factor Authentication (MFA)
MFA adds another layer of protection beyond passwords. It should be built-in or easily integrated into your environment. - Granular Access Control & Policy Enforcement
Look for systems that support role-based and context-aware access. This ensures users only reach what they’re authorized to—based on time, location, device, or risk. - Cloud Access Security Broker (CASB) Compatibility
Your provider should play well with cloud security tools, especially if you’re working in a multi-cloud or hybrid setup. - Seamless Integration with Existing Infrastructure
The best Zero Trust tools don’t force you to rebuild everything. They integrate smoothly with your current network infrastructure, directory services, and endpoint solutions. - AI-Driven Threat Detection and Context-Aware Access
Top-tier providers offer real-time risk assessment, adjusting access dynamically based on behavior patterns, device health, and threat intelligence.
Choosing a Zero Trust provider is about finding the right fit for your environment, risk tolerance, and security goals. The more adaptable and integrated the platform, the stronger your overall security posture becomes.
How Does Zero Trust Network Access (ZTNA) Actually Work?
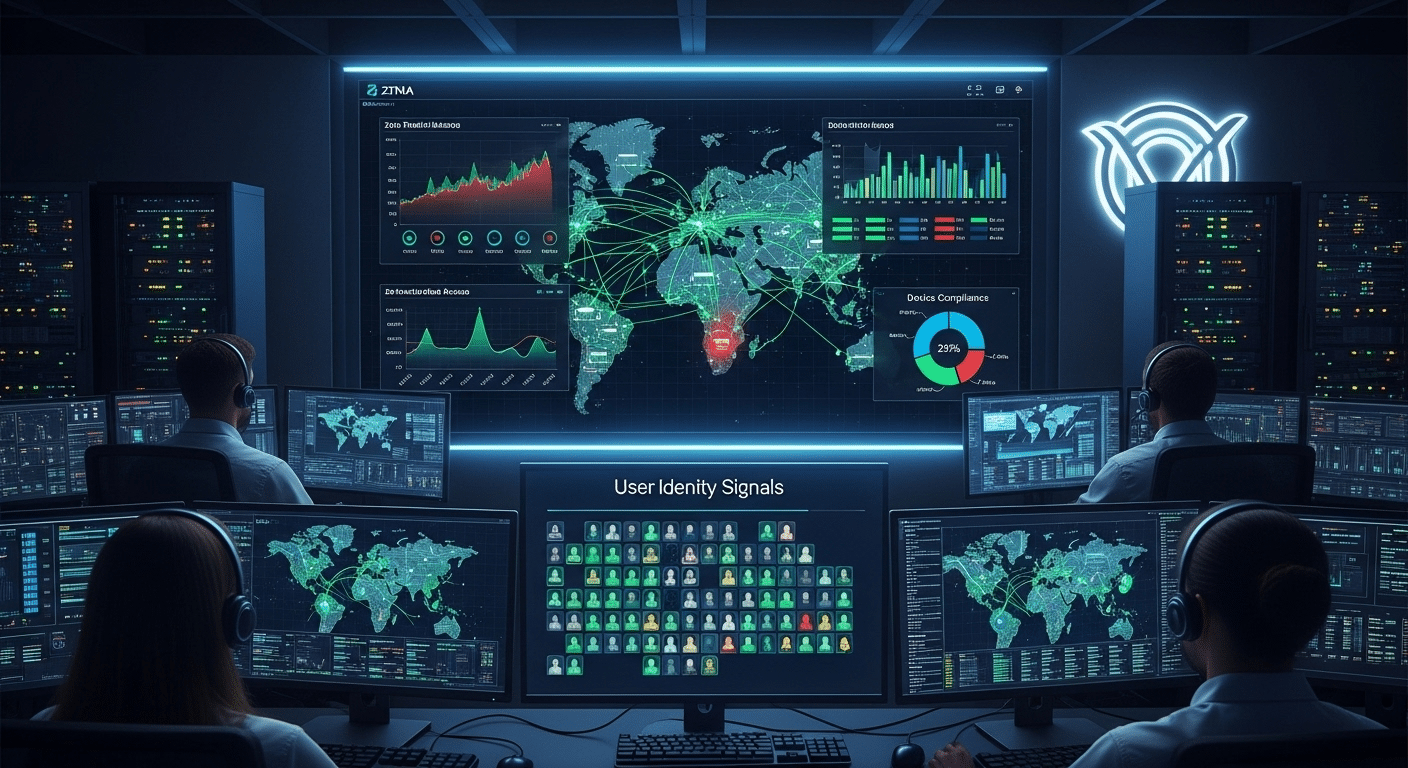
To understand Zero Trust Network Access (ZTNA), start with the basic idea: access is no longer tied to being “inside” a network. Instead, it’s tied to who you are, what you’re accessing, and how secure your device is.
Traditional VPNs gave users full network access once they connected. That worked when users and apps were inside a controlled perimeter.
But today’s apps are in the cloud, and users connect from everywhere. VPNs have become overly broad, clunky, and risky.
ZTNA replaces that model. Instead of exposing the network, it creates an invisible control layer. When a user tries to access something, ZTNA evaluates their identity, device status, location, and other contextual factors.
If the request meets policy, access is granted—to only that specific resource. Nothing more.
Here’s what makes ZTNA work effectively:
- Least Privilege Access
Users get only what they need, limiting exposure and reducing risk. - Continuous Verification
Trust isn’t permanent. Access is reevaluated constantly, especially if behavior changes or risk increases. - Device Security
ZTNA assesses whether a device meets security standards before granting access. - Trust Solutions vs Legacy VPNs
VPNs assume trust once inside. ZTNA assumes nothing. It’s dynamic, adaptive, and designed for the way modern work actually happens.
To conclude, ZTNA is the practical engine behind Zero Trust—controlling access not by location, but by validated identity and risk-aware policy.
What Security Features Should You Expect from a Top Zero Trust Vendor?
A strong Zero Trust vendor doesn’t just offer a few access controls—it delivers a comprehensive security solution that adapts to the evolving risk landscape. Here are the essential features you should expect:
1. Strict Access Controls Based on Identity, Device, and Context
Access should never be granted based solely on a password. Leading vendors use a combination of user identity, device health, and contextual factors (like time, location, and behavior) to determine who gets in—and what they can do.
2. Single Sign-On (SSO) and Risk-Based Authentication
Look for support for SSO to simplify logins without compromising security. In tandem, risk-based authentication assesses each login attempt in real time. If something looks unusual, it can trigger multi-factor authentication (MFA) or block access entirely.
3. Real-Time Continuous Risk Assessment
Top vendors don’t grant access once and forget about it. They continuously assess risk across sessions, adjusting access dynamically as conditions change. This is especially important for detecting compromised accounts or abnormal user behavior.
4. Adaptive Access Control Policies
Static rules no longer work. A good Zero Trust solution supports granular policy enforcement, allowing security teams to define who can access specific resources—under specific conditions.
5. Endpoint and Data Protection
The best platforms provide comprehensive protection for both devices and sensitive data. That means visibility into device posture, encryption, and secure access to applications whether they’re hosted in the cloud or on-prem.
To sum up, a top-tier Zero Trust vendor should make identity verification smarter, access management simpler, and security posture stronger—without adding unnecessary complexity to your environment.
Who Are the Top Zero Trust Security Providers Today?
Finding the right Zero Trust solution means matching your organization’s goals with a provider that aligns with your infrastructure, users, and security requirements. Below are the top Zero Trust vendors today, each with a unique strength and focus area.
1. Apporto
Apporto takes a refreshing approach to Zero Trust by focusing on simplicity, usability, and secure virtual desktop infrastructure (VDI).
Unlike heavy solutions built for sprawling enterprise environments, Apporto is tailored for higher education, SMBs, and teams that want quick wins without sacrificing security. Its browser-based VDI platform offers built-in ZTNA, secure remote access, and session isolation—all without the need for complex deployment.
Admins can define granular access policies, monitor sessions in real time, and apply least privilege access effortlessly. It also integrates with major identity providers, enabling smooth IAM workflows.
Apporto is ideal for organizations seeking a cost-effective, low-maintenance Zero Trust platform that just works—out of the box. Try Apporto Now
2. Zscaler (Zscaler Private Access)
Zscaler is a pioneer in cloud-native Zero Trust Network Access. Its platform replaces traditional VPNs with a fully distributed architecture, enabling secure, direct-to-app connections—no network exposure required.
Main features include ZTNA, AI-powered threat intelligence, and integrations with identity providers for fine-grained policy enforcement. It also provides secure access across multi-cloud environments and remote workforces.
Best for large enterprises needing deep cloud security capabilities and real-time traffic inspection at scale.
3. Palo Alto Networks (Prisma Access)
Prisma Access by Palo Alto Networks extends the company’s renowned firewall and threat detection technology into the Zero Trust space.
It delivers end-to-end Zero Trust architecture, from identity-aware access controls to advanced threat intelligence and data loss prevention.
Backed by their AI-powered Cortex engine, it provides risk-based authentication, deep user behavior analytics, and tight integration with other security tools.
Ideal for enterprises seeking a full-stack security solution that combines traditional perimeter defense with modern ZTNA.
4. Okta (Customer Identity Cloud)
Okta is considered the gold standard in identity and access management. With a laser focus on user identity, it enables fine-tuned control over who gets access, when, and under what conditions.
Features include adaptive MFA, SSO, granular policy enforcement, and detailed access logs. Okta’s strength lies in its massive ecosystem of integrations and developer-friendly architecture.
It’s especially strong for companies that need to manage customer or partner identities in addition to employees.
Best for teams implementing identity-first Zero Trust strategies with scalability and flexibility in mind.
5. Cisco (Duo + Secure Access by Cisco)
Cisco has made Zero Trust implementation accessible to a broader range of organizations through tools like Duo Security and Secure Access by Cisco.
It focuses on strong access management, endpoint visibility, and multi-factor authentication, ensuring users and devices meet your security standards before granting access.
Cisco’s strength lies in supporting hybrid environments where legacy infrastructure must coexist with modern cloud services.
It’s a smart choice for organizations looking to transition gradually into Zero Trust while maintaining a strong network security baseline.
6. Microsoft Entra ID (formerly Azure AD)
Microsoft’s Entra ID platform, previously known as Azure Active Directory, is deeply integrated across the Microsoft ecosystem.
It enables organizations to apply conditional access policies, MFA, SSO, and privileged access controls for both cloud and on-prem apps.
Built-in analytics help identify risky sign-ins and enforce access policies in real time. For Microsoft-heavy environments, it offers seamless integration and consistent security posture across services.
Ideal for organizations already invested in Microsoft 365, Azure, or hybrid enterprise IT stacks.
7. Cloudflare Zero Trust
Cloudflare’s platform combines network-level controls, ZTNA, browser isolation, and a secure web gateway into a single interface.
Its global network ensures fast performance with minimal latency, even for remote users. Admins can create granular access control policies and monitor traffic without backhauling data to a central data center.
Cloudflare stands out for its scalability and ease of deployment, particularly for organizations with distributed or mobile-first teams.
Best for businesses that need a lightweight Zero Trust solution with excellent edge performance and fast onboarding.
8. Check Point Software Technologies
Check Point delivers a comprehensive security stack, ideal for large enterprises and highly regulated industries.
Its Zero Trust capabilities span ZTNA, threat prevention, data loss protection, and endpoint security. Deep packet inspection, unified policy management, and real-time risk detection are part of the standard offering.
Check Point is especially strong in data protection, making it a fit for finance, healthcare, and government sectors.
Recommended for teams seeking tight compliance, fine-grained control, and enterprise-grade visibility across multiple domains.
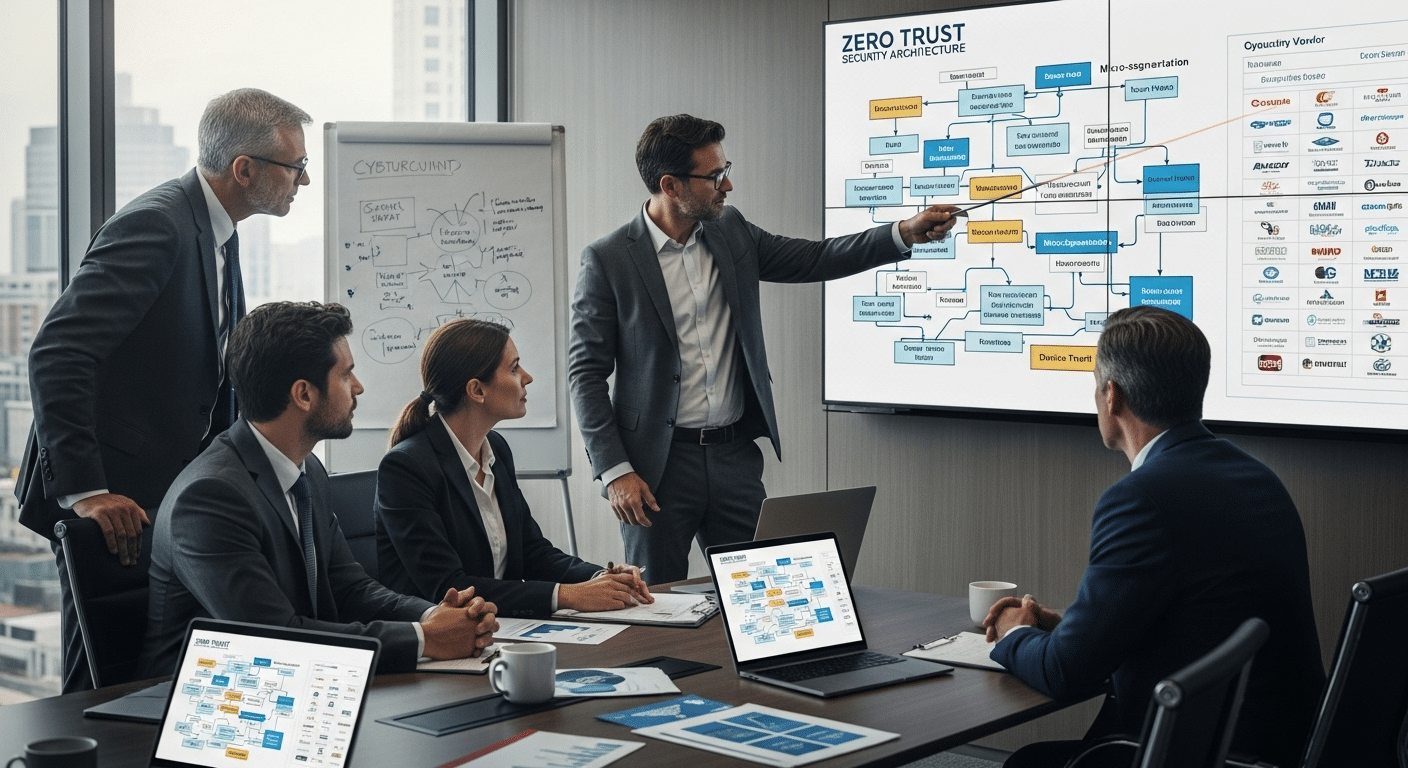
How to Choose the Right Zero Trust Provider for Your Organization
Choosing a Zero Trust provider isn’t just a technical decision—it’s a strategic one. Start by looking inward.
What does your existing infrastructure look like? Are you cloud-native, hybrid, or still relying heavily on on-prem systems? Your provider needs to align with that reality, not fight against it.
Next, assess your identity and access management (IAM) workflows. Do you already use a centralized identity provider like Okta or Microsoft Entra? How complex are your access control needs across departments, roles, and devices?
Then, consider your data protection goals. If your organization handles sensitive data—in education, healthcare, or finance—you’ll need vendors that support granular policy enforcement, privileged access controls, and strong encryption protocols.
Finally, think about the long game. A good provider should offer:
- Seamless integration with your stack
- Full visibility into user and device behavior
- Strong threat response and risk assessment tools
Prioritize flexibility, ease of use, and scalability. The right Zero Trust solution will not only enhance your security posture—it’ll also streamline your operations.
Is Zero Trust Overkill for Small and Mid-Sized Organizations?
It’s easy to assume Zero Trust is only for massive enterprises or government agencies. That’s a myth. In reality, small and mid-sized organizations often face the same cybersecurity risks—just with fewer resources to manage them.
The core principles of Zero Trust—like multi-factor authentication (MFA), least privilege access, and context-aware controls—are scalable by design.
You don’t need a team of engineers to implement them. You just need a platform that fits your size and workflow.
That’s where vendors like Apporto shine. With its lightweight, browser-based platform, Apporto enables secure access and ZTNA out of the box—no major infrastructure overhaul required.
It’s ideal for educational institutions, remote teams, and SMBs looking to modernize security without overwhelming their IT staff.
Zero Trust doesn’t have to be expensive, complicated, or enterprise-only. It’s about creating smarter controls that reduce risk—no matter your size. In today’s world, every organization needs to treat access as a risk. And Zero Trust is how you do it.
What Are the Risks of Choosing the Wrong Zero Trust Vendor?
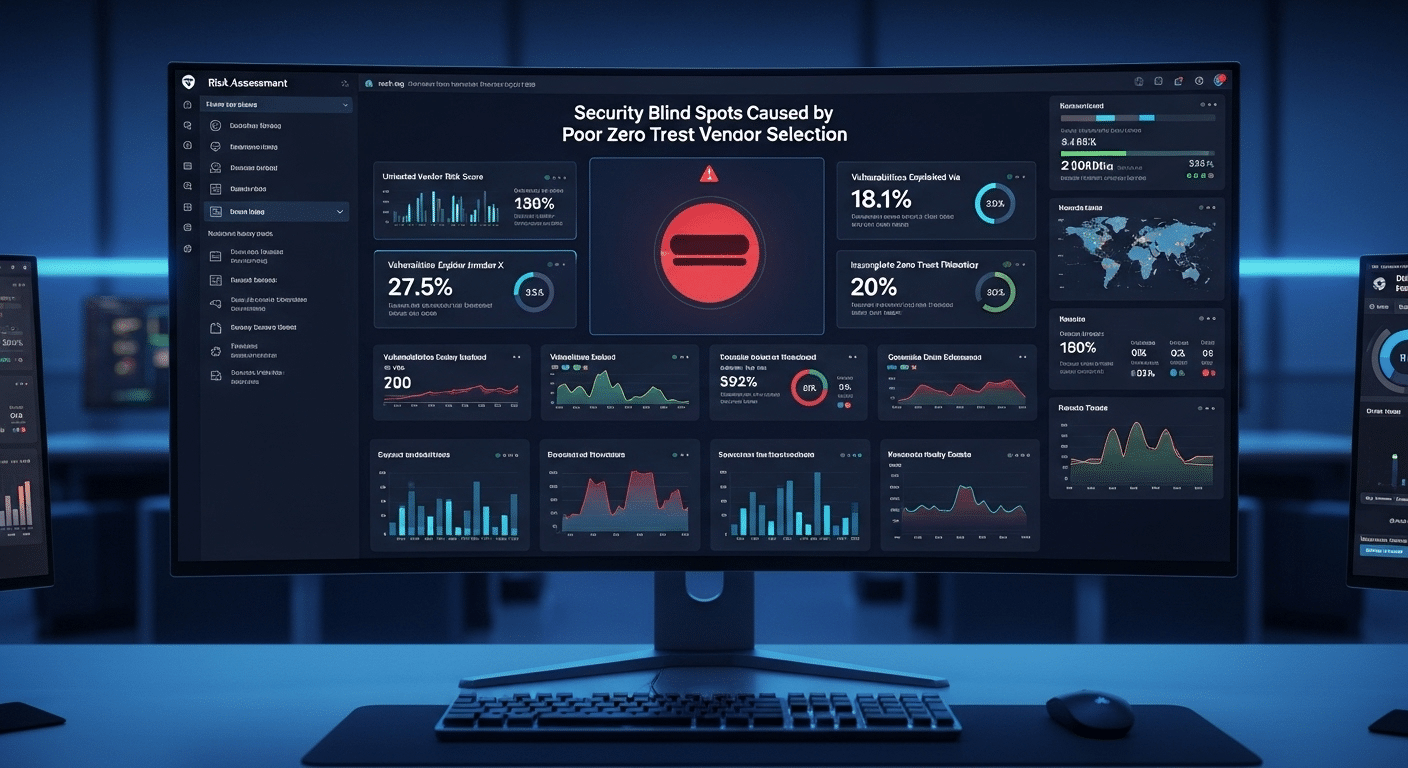
Zero Trust is powerful—but only when done right. Choosing the wrong provider can introduce more problems than it solves.
One major risk is vendor lock-in. Some platforms force you into using only their tools, limiting flexibility and increasing long-term costs. You may also face tool fatigue, managing multiple overlapping systems that don’t integrate well.
Poor compatibility with identity providers can disrupt access management and lead to inconsistent policy enforcement. And overly complex platforms can bog down your team, reducing productivity and creating security blind spots.
Worse, some solutions may leave gaps in cloud security or offer weak remote access controls—undermining the very foundation of Zero Trust.
Avoid these pitfalls by choosing a vendor that supports open standards, integrates with your stack, and aligns with your organization’s size, needs, and risk profile.
Final Thoughts
Zero Trust isn’t just a security product—it’s a security mindset. It’s about building a trust model based on identity, context, and verification, not assumptions. With threats growing more complex and networks expanding beyond office walls, the need for smart access control has never been more urgent.
Choosing a Zero Trust provider means choosing a long-term strategy for how your organization grants access, protects data, and responds to risk. It’s not a switch you flip overnight. It’s a gradual shift, and the right platform will help you make that transition with minimal friction.
If you’re looking for a solution that’s powerful but also practical, Apporto stands out. Its browser-based VDI platform brings Zero Trust principles to life with built-in ZTNA, secure access, and low overhead—perfect for education, SMBs, or any team seeking lightweight, scalable security.
Start evaluating. Test what fits. Trust should be earned—and Zero Trust helps ensure it is.
Frequently Asked Questions (FAQs)
1. What’s the difference between ZTNA and VPN?
ZTNA grants access to specific applications, not entire networks like a VPN. It continuously verifies identity and device health, reducing lateral movement and exposure.
2. Is Zero Trust really needed if I already use SSO and MFA?
SSO and MFA are important, but Zero Trust goes further. It adds context-aware policies, continuous verification, and granular access controls, reducing risks that basic login tools can’t cover.
3. Can Zero Trust help protect cloud and hybrid environments?
Absolutely. Zero Trust is built for multi-cloud and hybrid setups, allowing organizations to protect resources regardless of where users or data reside. It adapts to modern IT environments.
4. How long does Zero Trust implementation usually take?
It varies. Small teams can start seeing results in weeks by securing high-risk areas first. Larger deployments might take months, especially when integrating with existing infrastructure and policies.
5. Do I need a separate Zero Trust vendor if I use Microsoft 365?
Not always, but many organizations layer specialized Zero Trust tools on top of Microsoft 365. Vendors like Apporto offer secure access environments that complement Microsoft’s identity and cloud controls for more targeted protection.

