Universities weren’t built with restriction in mind. They were built to share, to connect, to explore ideas without too many barriers. That openness still exists, but now it comes with a cost that’s harder to ignore.
Each university faces over 2,500 cyber attacks every week, and incidents have surged by 114% in recent years. Nearly 74% of those attacks succeed. Not all are catastrophic, but enough are to cause real disruption.
At the center of it all sits valuable data, student records, financial data, research projects, intellectual property. Add remote learning, personal devices, and cloud-based tools, and the exposure grows wider than most systems were designed for.
In this blog, you’ll explore the risks, challenges, and practical ways to strengthen cybersecurity for universities.
Why Are Universities Such Attractive Targets for Cybercriminals?
Universities are built to be open. Ideas move freely, systems connect across departments, and access is often easier by design. That openness, while necessary for learning and research, creates conditions that attackers quietly rely on.
Most campuses don’t operate as a single, tightly controlled system. Instead, you get distributed higher education networks, different departments running their own tools, their own management systems, sometimes even their own rules. Over time, small inconsistencies turn into visible gaps. Not dramatic at first, but enough.
The numbers reflect it. Even a few years ago, universities were seeing over 1,600 cyber attacks each week. Now the pressure is constant, and in 2023 alone, 79% of institutions reported ransomware incidents. That’s not occasional exposure, it’s sustained targeting.
Then there’s the data. Universities hold a mix that’s unusually valuable, student records, financial aid information, sensitive research tied to grants, and intellectual property that can take years to develop. Some of that research, especially government funded work, attracts attention from nation-state actors. Quietly, persistently.
The technical side doesn’t make it easier. Legacy systems still running, third-party vendors introducing supply chain risks, remote learning platforms added quickly when demand surged. Add personal devices and cloud services, and the attack surface spreads wider than expected.
What Types of Cyber Threats Do Universities Face Most Often?
If you look at how attacks actually unfold, there’s a pattern. Different methods, same intent, get in, move quietly, extract value, or disrupt enough to force a response.
Most common cybersecurity threats universities face:
- Ransomware Attacks: Disrupt operations by encrypting critical systems and data, often bringing entire departments or campuses to a halt, with average costs around $2.73 million and recovery stretching longer than expected.
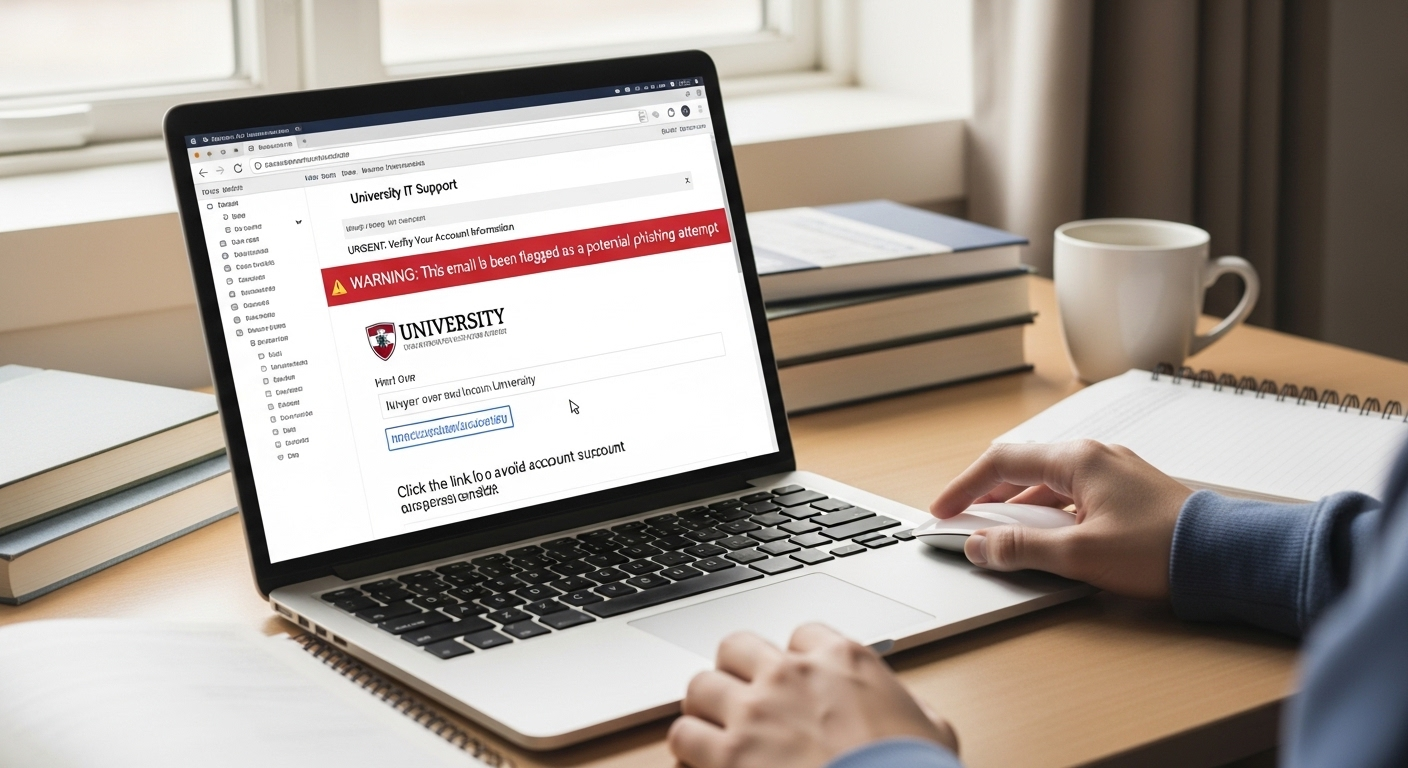
- Phishing Attacks: The most common entry point, with 97% of universities reporting phishing attempts that target user accounts through emails that feel routine, almost harmless, until they aren’t.
- Data Breaches: Expose student data, financial records, and research data, costing institutions between $3.65 and $3.7 million on average, with long-term reputational damage that doesn’t show up immediately.
- Distributed Denial of Service (DDoS): Overload university networks with traffic, disrupting learning management systems, portals, and essential digital services at critical times. Timing matters here.
- Research Espionage: Targets sensitive research and intellectual property, often involving foreign actors or external research partners, with goals that extend beyond immediate financial gain.
- Insider Threats: Result from human error or misuse of access, sometimes accidental, sometimes intentional, but often difficult to detect early.
- AI-Driven Cyber Attacks: Use AI to automate phishing campaigns and malware distribution, making attacks faster, more convincing, and harder to filter out.
What Types of Data Are Universities Trying to Protect?
You don’t really see the full picture until you list it out. Universities aren’t holding one kind of data, they’re holding many, layered across systems that weren’t always designed to work together neatly.
Start with student records and personally identifiable information, names, identification numbers, academic history, sometimes even behavioral data. Then there’s financial aid information, income details, banking data, payment records, the kind of information that can be misused quickly if exposed.
Add health data, especially in institutions with medical programs or campus health services. That introduces another level of sensitivity, and legal responsibility too.
Then come the systems themselves. Institutional and digital systems, admissions platforms, learning management systems, administrative tools, all storing and processing data continuously. If those systems are compromised, the impact spreads wider than expected.
And then, quietly, there’s research data and intellectual property. Years of work, sometimes tied to government funding or external partnerships. This is where attention from more advanced actors begins to show.
Regulations attempt to keep structure around all this. FERPA governs student records. GLBA focuses on financial data. GDPR applies when dealing with international users. The privacy act adds another layer depending on jurisdiction.
But breaches don’t separate things cleanly. They often expose multiple data types at once.
That’s why protecting these critical assets requires strict access controls and encryption, not occasionally, but consistently.
What Makes Cybersecurity So Challenging for Universities?

You might expect large institutions to have this figured out. Resources, structure, expertise. But the reality is a bit uneven, sometimes surprisingly so.
Start with budgets. Universities often operate under tight financial constraints, and cybersecurity doesn’t always get priority over visible initiatives like research funding or campus expansion. The risk, though, doesn’t shrink to match the budget. It keeps growing quietly in the background.
Then there’s the talent gap. Skilled cybersecurity experts are in short supply, and universities don’t always compete well with private sector salaries. So teams stay small. Sometimes stretched thin. And that has consequences.
Recovery times tell part of the story. Around 40% of institutions take more than a month to recover from a cyber attack. That’s not just a technical issue, it’s operational disruption, classes affected, research delayed, systems offline longer than expected.
Structure adds another layer. Governance is often decentralized, departments managing their own systems, their own tools, sometimes their own policies. Over time, this creates inconsistency. Not dramatic at first, but enough to weaken the overall security posture.
And then there are the systems themselves. Legacy systems, older operating systems that still support critical applications, but aren’t built for current threat levels. Maintaining them becomes a balancing act. Necessary, but risky.
How Do Cybersecurity Frameworks Help Universities Strengthen Security?
Frameworks like NIST SP 800-171 and CMMC were designed to help institutions handle sensitive data, especially when working with federal government agencies or government funded research. They set expectations. Not vague ones, but specific controls around how data is stored, accessed, and protected.
What makes them useful is the risk-based approach. Instead of treating every system the same, you assess what’s most critical, research data, financial systems, administrative platforms, and apply stronger protections where the stakes are higher. It’s a way of prioritizing, rather than spreading efforts thin.
There’s also the compliance layer. Universities that interact with federal programs are required to meet certain standards, and failing to do so can lead to penalties or loss of funding. So frameworks don’t just guide security, they define eligibility in some cases.
But structure alone isn’t enough. Governance matters. Advisory committees, collaboration between IT teams and research faculty, those conversations help balance security with usability.
Over time, frameworks reduce gaps. Not instantly, but steadily. And they give universities something they often lack, a consistent direction.
What Cybersecurity Best Practices Should Universities Implement?

Risks don’t come from one place, and they don’t stay contained. So the response can’t be fragmented either. It has to be layered, consistent, and, in a way, a little relentless.
Here’s what effective cybersecurity for universities requires:
- Multi Factor Authentication: Protect user accounts and prevent unauthorized access by adding an extra layer of identity verification, one of the simplest and most effective ways to stop credential-based attacks.
- Identity and Access Management: Enforce strict access controls and role-based access so users only interact with systems and data necessary for their role, reducing unnecessary exposure.
- Network Segmentation: Isolate research, financial, and administrative networks from general student access, limiting how far an attacker can move within the university’s network.
- Data Encryption: Protect sensitive data during storage and transmission, ensuring that even if data is intercepted, it cannot be easily read or misused.
- Incident Response Plan: Develop and test clear response procedures so teams can detect, contain, and recover from cyber incidents without confusion or delay.
- Regular Risk Assessments: Identify vulnerabilities through audits, reviews of access controls, and continuous monitoring before they are exploited.
- Security Awareness Training: Teach users to recognize phishing attempts and unsafe behavior, since human error remains one of the most common entry points.
- Zero Trust Model: Apply a “never trust, always verify” approach, where every access request is validated regardless of location or prior access.
- Patch Management Automation: Apply security patches quickly to operating systems and applications, reducing exposure from outdated systems.
- Backup Strategy (3-2-1-1 Rule): Maintain multiple secure backups, including isolated and immutable copies, to recover quickly from ransomware attacks.
How Does Cybersecurity Awareness Reduce Human Risk?
Most breaches don’t begin with complex code or advanced tools. They begin with people. A click that felt harmless, a password reused one too many times, a message that looked familiar enough to trust. Human error sits at the center of many security incidents, quietly, repeatedly.
In universities, this becomes more pronounced. You have students, faculty, administrative staff, all interacting with systems differently. Different habits, different levels of awareness. That variation creates opportunity.
Training helps, but not in the way people often expect. It’s less about memorizing rules and more about recognition. When users start to notice subtle signs, unusual links, slightly off email addresses, odd timing, phishing attempts lose some of their effectiveness. Over time, the success rate drops. Not to zero, but enough to matter.
The key is consistency. Programs need to reach everyone, students, faculty, staff, and they need to feel relevant to how each group actually works. Otherwise, the lessons don’t stick.
And then there’s the broader idea. A shared responsibility culture. Because cybersecurity for universities doesn’t sit with one team alone.
It spreads across the institution, shaped by everyday decisions. Over time, that awareness becomes quiet protection, not perfect, but steady, and surprisingly effective.
How Do Cloud Services and Remote Learning Affect University Security?

Systems moved gradually into the cloud, storage first, then applications, then entire environments. At the same time, remote learning expanded, sometimes faster than anyone expected. And suddenly, access wasn’t tied to campus anymore. It was everywhere.
Cloud platforms bring clear advantages. Scalability is one of the most obvious. You can expand resources as demand grows, research workloads increase, enrollment fluctuates. Then there’s flexible access, students and faculty can connect from almost any device, any location, without needing specialized hardware. That flexibility matters.
Relying on cloud services introduces third-party vulnerabilities. If a provider has a weakness, it doesn’t stay isolated. It becomes part of your environment. Then there’s data residency, where data is stored, how it’s handled, and whether it meets regulatory requirements. These details tend to get overlooked until they become a problem.
Remote learning adds another layer. More devices, more connections, more entry points. Many of those devices aren’t managed by the institution, which increases uncertainty. The attack surface expands quietly, but significantly.
Strong security strategies, access controls, encryption, monitoring, become essential. Not as enhancements, but as the baseline needed to keep systems reliable as they extend outward.
How Are AI and Emerging Technologies Changing University Cybersecurity?
Something interesting is happening, quietly, almost in the background. Security systems are getting faster, more aware, less dependent on fixed rules. And at the same time, attackers are evolving in similar ways.
On the defensive side, AI-driven monitoring and detection is becoming more common. Instead of waiting for known threats, systems can now analyze patterns, spot unusual behavior, and flag risks early. Not perfectly, no system is, but earlier than before. That timing matters.
You also see more continuous monitoring tools in place. These don’t just check systems occasionally, they observe constantly, looking for small signals that something might be off. A login at an unusual time, a sudden change in data access, subtle things that would be easy to miss manually.
But the same technology is being used by attackers. AI is helping create more convincing phishing messages, automate attacks, and scale them faster than traditional methods allowed. Messages feel more natural now, harder to question.
So the balance keeps moving. Cyber threats aren’t static. They adapt, and sometimes faster than expected.
How Can Universities Balance Accessibility with Security?
There’s a tension here that never quite goes away. Universities are built around access, open systems, shared knowledge, collaboration across departments and even across borders. But security, by nature, introduces friction. And too much friction, well, it starts to interfere with how people work.
You don’t remove access, you refine it. Role-based access is part of that, giving users only what they need, not everything that happens to be available. It sounds simple, but in practice, it requires constant adjustment as roles change, projects evolve, and systems expand.
Then there’s identity verification. Not just logging in once and moving on, but verifying access continuously, especially for sensitive systems or research environments. It adds a step, yes, but it also closes doors that would otherwise stay open.
What often gets overlooked is collaboration. IT teams and research teams don’t always operate in sync, but they need to. Decisions about access, data handling, and system design work better when both sides are involved.
Because in the end, it’s not about choosing between usability and protection. It’s about shaping both, carefully, so neither breaks the other.
Why Apporto Supports Secure Access for Universities?
Apporto takes a different route. It’s a browser-based platform, which means access happens through a controlled environment instead of relying on local machines. You log in, open what you need, and the system handles the rest behind the scenes. It feels straightforward, and that’s part of the point.
Because data stays centralized, the attack surface is reduced. Sensitive information isn’t scattered across personal devices or unmanaged endpoints. At the same time, access can be controlled consistently, without depending on how each device is configured.
Final Thoughts
If there’s one thing that becomes clear over time, it’s this, reacting isn’t enough anymore. You can respond to incidents, patch systems, recover, but if the approach stays reactive, the same patterns tend to repeat. Just in slightly different forms.
Cyber threats are becoming more persistent, and in some cases, more subtle. They don’t always announce themselves loudly. Sometimes they sit quietly, waiting. That alone changes how universities need to think about security.
A more proactive strategy starts to matter. Anticipating risks, strengthening access controls, investing in monitoring and awareness before something goes wrong. Not after.
And yes, it requires commitment. Not a one-time investment, but something ongoing, built into how systems are designed and maintained.
Because over time, resilience doesn’t come from quick fixes. It comes from steady, deliberate effort that holds up under pressure.
Frequently Asked Questions (FAQs)
1. What is cybersecurity for universities?
Cybersecurity for universities refers to the strategies and technologies used to protect digital systems, student records, research data, and financial information. It focuses on preventing unauthorized access, securing networks, and ensuring that critical academic and administrative systems remain reliable and protected.
2. Why are universities targeted by cyber criminals?
Universities are attractive targets because they store valuable data and operate in open, decentralized environments. Large user bases, research projects, and distributed systems create multiple entry points, making it easier for attackers to find vulnerabilities and gain access to sensitive information.
3. What data is most at risk in universities?
The most at-risk data includes student records, personally identifiable information, financial aid data, health records, and research data. Intellectual property and institutional systems are also critical assets, and breaches often expose several types of data at the same time.
4. How can universities prevent ransomware attacks?
Prevention involves strong access controls, multi factor authentication, regular system updates, and secure backups. An effective incident response plan also helps limit damage, while monitoring systems and user awareness reduce the chances of ransomware entering through phishing attempts.
5. What role does training play in cybersecurity?
Training helps users recognize phishing attempts, suspicious activity, and poor security habits. Since human error is a leading cause of breaches, educating students, faculty, and staff plays a major role in reducing risks and strengthening overall cybersecurity practices.
6. Are cloud services secure for universities?
Cloud services can be secure when properly configured. They offer scalability and centralized management, but also introduce risks such as third-party vulnerabilities and data residency concerns. Strong access controls, encryption, and monitoring are essential to maintaining security in cloud environments.
7. What are cybersecurity frameworks for universities?
Cybersecurity frameworks provide structured guidelines for managing security risks. Examples include NIST and CMMC, which help universities protect sensitive data, meet compliance requirements, and improve their overall security posture through standardized practices and risk-based approaches.

