Companies across various sectors—technology, healthcare, finance, and retail—are declaring themselves “AI-first,” signaling a strategic shift to prioritize AI in their operations, decision-making, and innovation practices. This means embedding AI into core processes to enhance productivity, efficiency, and innovation. For example, Google has prioritized AI technologies in its products, from search algorithms to autonomous driving projects. Similarly, Amazon uses AI to optimize supply chains and personalize customer experiences.
Beyond tech giants, AI is penetrating traditional industries. In healthcare, AI algorithms assist in diagnosing diseases and personalizing treatments. Financial institutions use AI to detect fraudulent transactions and forecast market trends. Retailers leverage AI for inventory management and customer insights. These applications demonstrate that AI is no longer a futuristic concept but a cornerstone of modern business strategy.
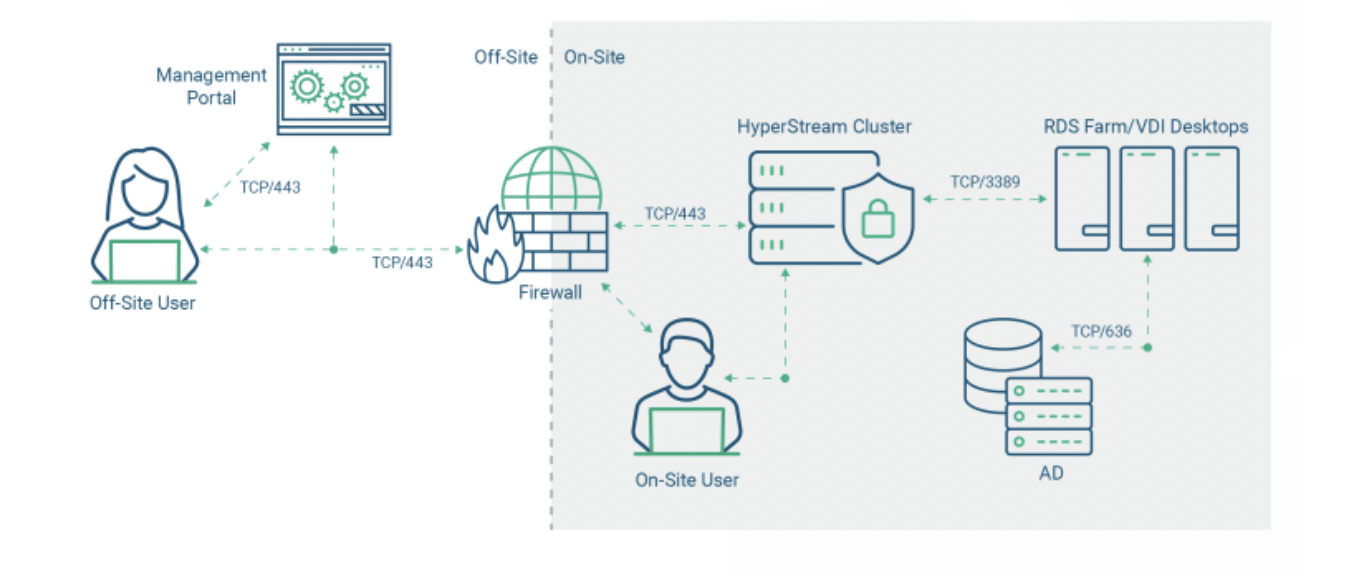
At Apporto, we have adopted a matrix that defines the maturity model of candidates for various jobs in the company. Here is the Engineering role maturity model. We give strong preference to those candidates who are in the adoptive or transformative stages.
Calls AI coding assistants ‘too risky’
Has never tested AI-generated codeUses ChatGPT/Copilot for simple coding tasks (e.g., regex, unit-test stubs)
Can explain how they prompt, review, and validate AI outputUses ChatGPT/Copilot for simple coding tasks (e.g., regex, unit-test stubs)
Can explain how they prompt, review, and validate AI output
Chains LLM calls with fallback + retry logic
Adds eval tests to flag hallucinations
Knows Claude Code, Cursor, Windsurf, etc.Ships LLM-powered features, monitors live metrics, and refines based on user feedback
Builds an AI-first dev pipeline (guardrails, RAG docs, etc.) that cuts down PR cycle time
| Unacceptable | Capable | Adoptive | Transformative |
|---|
The Case for Education to Lead the AI-First Revolution
While businesses are redefining themselves around AI, education—arguably the foundation of all industries—must not lag behind. The rapid adoption of AI in the corporate world underscores the necessity for educational institutions to rethink how they prepare students for the future. Here are compelling reasons why education must embrace an AI-first mindset:
-
Preparing Students for the Future Workforce
AI is reshaping the job market. Traditional roles are evolving, and new ones are emerging that require AI proficiency. To equip students for this new reality, education must integrate AI into curricula, from primary levels to higher education. Teaching students not only how to use AI tools but also how to build, understand, and question them ensures they are prepared to navigate an AI-driven world.
-
Enhancing Learning Experiences
AI has the potential to revolutionize the way students learn. Adaptive learning platforms, powered by AI, can personalize education to meet the unique needs of each student. Such approaches not only improve academic outcomes but also foster a love for learning by making it more engaging and relevant.
-
Reducing Inequality in Education
One of AI’s most promising applications is its ability to bridge gaps in education access. AI-powered tools can provide high-quality educational resources to underserved communities, overcoming barriers such as geographical distance and teacher shortages. For instance, virtual tutors and AI-driven learning apps can bring world-class instruction to remote areas, democratizing education in unprecedented ways.
-
Driving Institutional Efficiency
Just as businesses use AI to streamline operations, educational institutions can leverage AI for improved efficiency. AI can assist in teaching tasks such as tutoring, grading and providing feedback, and more.
Challenges and Opportunities
Adopting an AI-first approach comes with its challenges. Issues such as data privacy, algorithmic bias, and the digital divide must be addressed to ensure equitable and ethical implementation. However, these challenges also present opportunities for innovation. By involving diverse stakeholders—including students, educators, policymakers, and technologists—education can develop AI solutions that are inclusive and responsible.
Moreover, the AI-first transition in education is not just about technology; it is about a cultural shift. It requires an openness to experimentation, a willingness to adapt, and a commitment to lifelong learning. Educational institutions must foster an environment where curiosity and creativity thrive, empowering students to not only adapt to the AI era but to shape it.
Conclusion
The AI-first movement in industry is a clarion call for education to follow suit. As companies leverage AI to redefine success, educational institutions have an opportunity—and a responsibility—to redefine learning. By adopting an AI-first approach, education can prepare students for the future, enhance learning experiences, and contribute to a more equitable and ethical society. The time to act is now. The future of AI is not just about machines and algorithms; it is about people and possibilities. Let education take the lead in unlocking this future.